Blog
Aug09
Common Intrusion Points for Ransomware and Malware Infections
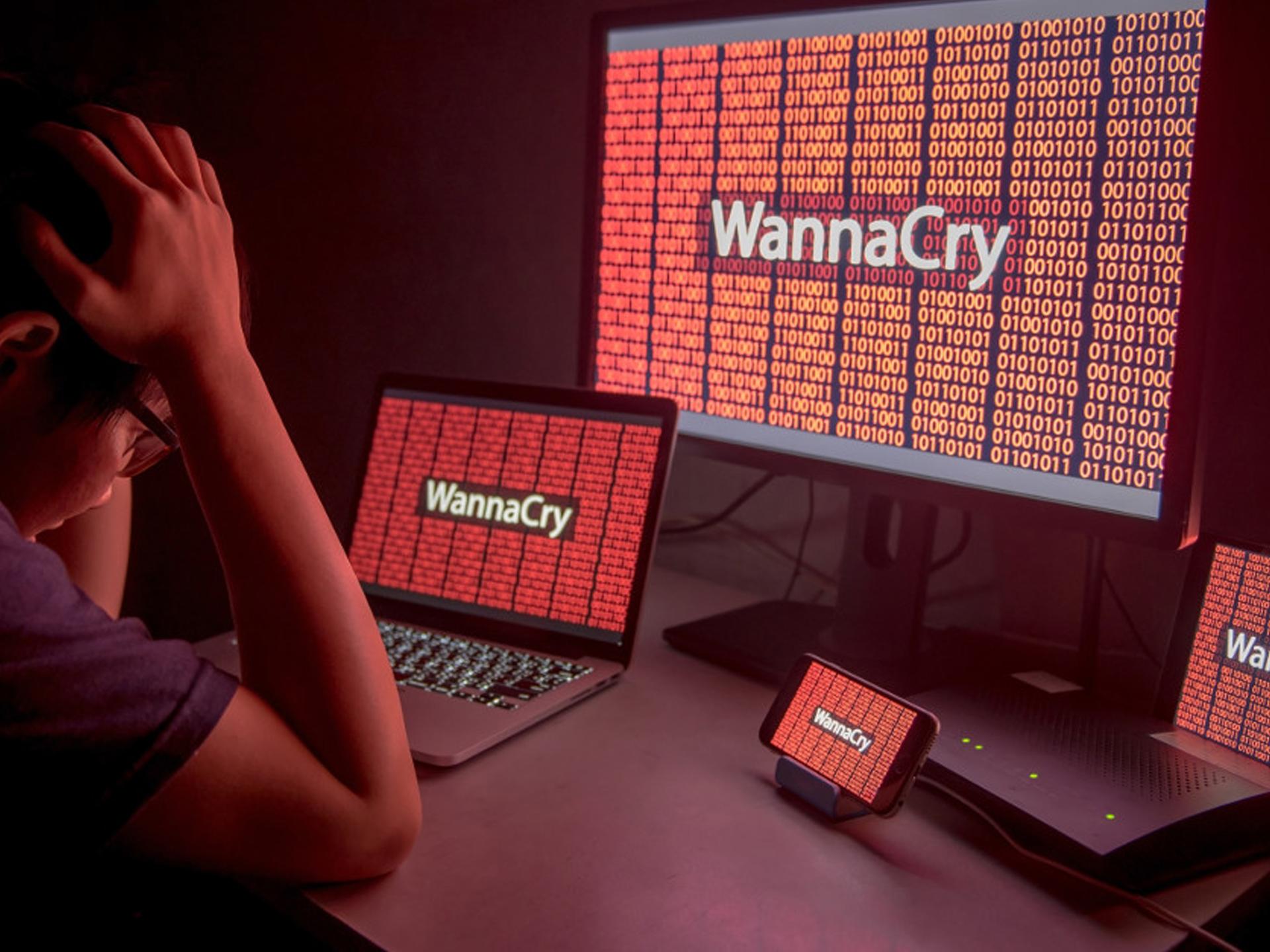
If you have read the news recently, you have probably heard of the WannaCry ransomware attack, a scary computer infection that took hold and quickly spread worldwide. In what seemed like a matter of hours, computers across the globe were crippled, as were the businesses that owned them.
As ransomware goes, the WannaCry exploit turned out to be somewhat impotent, with a small amount of money paid out in ransom and a relatively short-lived infection cycle. Even so, the writers of malicious software were taking notes, and they are already using the lessons of WannaCry to write newer, better and more damaging infections.
Whether you own a business or just a single computer, you need to take proactive steps to protect yourself and your files. That means to backup up your files regularly, keeping those backups off the network and using virus scans and malicious software detectors to find infections before they have a chance to harm you.
It is also important to identify common intrusion points for not only ransomware but other forms of malicious software as well. Once you know where the malicious code is coming from, it will be easier to protect yourself, your computer and your precious files.
Targeted Emails
While targeted emails are rarely used to spread ransomware, they are a common source of other malicious software. Employees, managers and individual computer owners should continue to view unsolicited emails with suspicion, and they should still avoid clicking links unless they are absolutely sure where the message originated.Business owners can protect themselves by installing robust spam filters and stripping out attachments whenever the sender is unknown. Managers can also train their staff on the dangers of malicious software and institute policies for fighting it.
Fake Software Update Sites
Fake software update sites are a common source of ransomware infection, and that makes them particularly dangerous. In these targeted attacks, users are confronted with pop-up windows or tabs that purport to offer updates to Adobe and other popular programs. What those sites really offer, however, is ransomware, and once the software is in place, it is just a matter of time before the attack begins.Businesses and individuals can protect themselves by checking the URL of all sites before downloading software updates. These sites may look genuine, but their addresses often give them away.
Business owners can also protect themselves by blocking Torrent sites, file sharing services and other sites where these fake software updates often originate. Blocking any site that lacks a legitimate business purpose is good practice and a good way to protect the company files from ransomware.
Bootlegged Operating Systems
Many victims of the recent ransomware attacks turned out to be running non-genuine versions of popular Windows operating systems. That is why countries like Russia and parts of Asia and Eastern Europe were so heavily represented in the attack.That does not mean, of course, that other countries are immune to this problem. Indeed, many individuals, and even some companies are running grayware software or other less than legitimate versions of Windows, Office and other popular programs.
The reason bootlegged and illegitimate software is such a problem is that it cannot be patched. The vulnerability exploited by the WannaCry ransomware attack was actually uncovered months earlier, but many users, especially those with bootlegged software, had failed to update their systems.
Unpatched Systems
Even owners of legitimate operating systems often fail to keep their systems up to date, leaving their computers and networks vulnerable to ransomware and malware attack. Some businesses worry that a faulty update will cripple their network, or that an update will interfere with the operation of an older piece of software. Individual users may worry that an update could damage their computer, or even render it inoperable.These fears are somewhat justified, but the fear or ransomware should be even greater. Missing even a single critical update could open the door to ransomware or other malicious software, so businesses and individuals can no longer afford to take security for granted.
Ransomware is not going away anytime soon, and businesses that fail to protect themselves are just asking for trouble. If you have not yet taken proactive measures to protect the company network, now is the time to get going. There are things business owners, managers, employees and individual users can do to blunt the danger of ransomware, and knowing where these attacks originate is a good first step.
Share This Post
Comments
Read Our Other Blog Posts.
© Copyright 2017 by Advanced Network Professionals. All Rights Reserved. | Web Design by 154i
