Blog
Data Recovery 101: Best Practices for Backing Up & Restoring Data
Effective data protection begins with a single step: understanding the foundation. Whether you’re a small startup or a large enterprise, the importance of data storage and data backup cannot be overstated.
These practices are your first line of defense against data loss, ensuring that your critical information remains accessible and secure.[...]
Read more.What To Do If You Suspect Your Business Has Been Targeted by Malware
These days, threats loom just a click away. That means protecting your business from malware is more critical than ever.
Slow computer performance, frequent popup ads, and unexplained data loss are just a few signs that your business might be under attack. Ignoring these warning signs can lead to significant losses and compromise the safety of[...]
Read more.What Is Multi-Factor Authentication (MFA) & How Does It Protect Business Data?
In an era where data breaches are as common as morning coffee, it’s more important than ever to understand how to safeguard sensitive business data. Multi-factor authentication (MFA) is a powerful tool that adds an extra layer of data security by requiring more than just a password to access your systems.
Whether it’s through[...]
Read more.How Outdated Operating Systems Pose Security Risks to Your Business
In today’s fast-paced digital world, the importance of staying updated with the latest operating systems cannot be overstated. While it might seem like a minor inconvenience to delay updates, the reality is that outdated operating systems can expose your business network security to significant risks.
These risks include vulnerabilities[...]
Read more.Why Penetration Testing Helps Prevent Successful Cyber Attacks
In the ever-evolving landscape of cybersecurity, understanding the role of penetration testing is crucial for safeguarding your digital assets.
As cyber threats become more sophisticated, businesses need to stay ahead of potential cyber attacks by identifying and addressing vulnerabilities before malicious actors can exploit them. Penetration[...]
Read more.How to keep your business's network - and the data it contains - secure from malicious actors
In today’s digital landscape, safeguarding your network is more critical than ever, and understanding where your defenses are weakest is the first step. With the ever-increasing sophistication of cyber threats, network security must be a top priority.
To ensure your business is protected, it’s essential to follow network security best[...]
Read more.Why a Managed IT Services Providers Could Be a Game-Changer for Your Business
In today’s digital landscape, small businesses face unique challenges that managed IT services are uniquely positioned to address. From ensuring 24/7 system monitoring to providing advanced cybersecurity, these services can significantly boost productivity and protect your valuable data.
By outsourcing IT, you can focus on your core[...]
Read more.Why employees must be prepared to respond to a malware attack against your organization
Today, the threat of malware is more real than ever, with new and sophisticated strains constantly emerging. A single virus or ransomware attack can not only drain your finances but also severely damage your company's reputation and customer trust. To stay ahead, it's crucial to understand the evolving malware threat landscape and to have a[...]
Read more.How to train employees to recognize and report phishing attempts
In today's digital landscape, one of the most pressing threats to a business's security is phishing. These deceptive tactics are designed to trick employees into divulging sensitive information, potentially compromising the entire organization. The first line of defense against such attacks is a well-informed workforce. This guide will explore how[...]
Read more.Cybersecurity tips for keeping customer and company data safe and secure
Businesses today encounter an increasing number of cybersecurity threats that can compromise customer data and other sensitive information. As cyberattacks become more sophisticated, it's crucial for organizations to prioritize data security. We’ve covered why cybersecurity is important recently, but this comprehensive blog post will go[...]
Read more.Why businesses need to take data security seriously to protect their customers, employees and business
In today's digital age, businesses of all sizes are facing an unprecedented threat from cyberattacks. With the increasing sophistication of cybercriminals and the potential for devastating financial and reputational damage, it's no longer a question of if your business will be targeted, but when.
That’s why we have compiled this overview[...]
Read more.What is a firewall and how does it keep my company's data secure?
In today's digital landscape, protecting sensitive company information and data is paramount. Firewalls serve as a critical line of defense against cyber threats, safeguarding your organization from unauthorized access, denial of service attacks, and malware.
This comprehensive guide will delve into the intricacies of firewalls, explaining how[...]
Read more.How do I protect my business's data from cryptolocker malware?
CryptoLocker malware is a severe threat to businesses of all sizes, capable of encrypting critical files and demanding ransom payments for their release. This article aims to provide a comprehensive guide to safeguarding your business's data from the clutches of CryptoLocker.
We will delve into its mechanisms, infection vectors, and the crucial[...]
Read more.What employeers and employees must know to protect businesses from phishing attacks
Phishing is a type of cyber attack that uses disguised emails as a way to steal personal information. Phishing emails often look like they're from a legitimate source, such as a bank or a government agency, and they may contain links to fake websites that look like the real thing. If you click on a link in a phishing email, you could be giving up[...]
Read more.Why a managed IT service provider may make the most sense for your small business
Technology plays a crucial role in the success of any business, regardless of its size. However, managing and maintaining IT infrastructure can be a complex and time-consuming task, especially for small businesses with limited resources and expertise.
This is where managed IT service providers come in. They offer a comprehensive range of IT[...]
Read more.Why small businesses should be concerned about malware
As the world grows increasingly digital, small businesses are more vulnerable than ever to malicious cyber-attacks.
Unfortunately, many of these businesses lack the resources or expertise to fully protect their digital assets from malware and other forms of attack. The risks associated with malware are immense and should not be taken[...]
Read more.Why updated software is critical for running a successful business
Keeping small business software up to date keeps your business running efficiently and securely. Software updates can provide a range of benefits, including improved performance, increased security, and new features. But it’s important to know when and how to update software correctly, as well as what services are available to help.
Let's[...]
Read more.How penetration testing can identify security gaps in your business's network
Securing business data should be a top priority for organizations of all sizes. Cyberattacks are constantly evolving and becoming more sophisticated, making it essential for companies to stay up-to-date on the latest security measures.
Penetration testing is an effective tool that can be used to identify and fill network security gaps, ensuring[...]
Read more.Why data security is important and how a managed IT service provider can help
Data security is a critical element of any business, and one that should not be taken lightly.
With the ever-increasing threat of cyberattacks and data breaches, it is essential for businesses to take proactive steps to protect their data and secure their networks.
There are a number of simple, basic proactive steps that businesses can do to[...]
Read more.Why you should hire out IT relocation services
Moving a business can be exciting. In many cases, the reason for the move is positive. Your business or organization likely is experiencing growth, either in space needed for added personnel and hires or you’re expanding to another location.
In both scenarios, congratulations are in order. However, moving can be incredibly stressful,[...]
Read more.Protect your small business from email phishing attacks
The majority of people with email accounts have encountered phishing emails and other forms of spam at some point, especially to work email accounts.
There are approximately 45 percent of emails sent each day that are spam. According to Spam Laws, there are an estimated 14.5 billion spam messages sent every day.
It is common for email clients to[...]
Read more.Your business's network has been attacked by malware. Now what?
Cyber attacks are an unfortunate reality for small businesses.
In fact, it can be argued that small businesses especially should be aware of how often they are at risk of being targeted by a cyber attack. According to Fundera, 43% of cyber attacks go after small businesses. Of those businesses that fall victim to these attacks, 60% go out of[...]
Read more.What is a firewall and does my business need one?
Your business’s data has never been more important – nor has it ever been more valuable.
The data your business collects and stores not only contains critical internal information pertaining to operations and processes, but likely also contains private customer information. Should any of this data be accessed by unauthorized[...]
Read more.How can I stay safe from crypto locking?
Read more.
HOW SECURE ARE MY DATA BACKUP AND RECOVERY SYSTEMS? DO I NEED HELP?
A secure data and recovery system is key to the sustainability of the business. Imagine a fire breaks out at your office and burns it down. How long will it take you to recover and get back to business? You might have insured your business against such an instance, but how do you get back all the data you have taken years to build? It is,[...]
Read more.7 Tips to Enhance Network Performance
Learn about the triggers of poor network performance and how to mitigate them for your team to enjoy optimal network performance and enhanced productivity.
A seamless network performance results in productivity and efficiency. The cost of a failing network is loss of productivity and downtime. Business continuity is critical to all businesses,[...]
Read more.Preventing Ransomware Attacks is now More Important for Organizations than Ever.
Ransomware attacks are on the rise as cybercriminals turn to savvier and tougher-to-prevent techniques of monetizing cyberattacks. For not-for-profit and business organizations that become victims of these attacks, both financial and ethical consequences can be devastating. Let’s put things in perspective; if ransomware lands in a shared[...]
Read more.5 Ways your Business can benefit from IT Managed Services
An increasing number of both for-profit and not-for-profit organizations are enlisting IT managed services, and it’s not hard to understand why. Today’s business landscape is becoming more reliant on information technology (IT). Many organizations realize that they can optimize operational costs while outpacing the competition,[...]
Read more.5 tips for how to keep your small business network more secure
It’s certainly no understatement to say many of today’s businesses rely on a network to maintain a connection between shared devices, coworkers’ computers and, in some cases, even their customers’ devices. But the more devices, hardware and software that rely on a business’s network connection, the more susceptible[...]
Read more.This is why you should always backup your businesses's data
Data is everything in today’s business world.
Think about it: Businesses of every size, from the largest corporations to small one-man or mom and pop operations, rely on data to keep their businesses successful and growing.
This is why it is absolutely imperative for all businesses to have a reliable way to not only keep data secure, but[...]
Read more.What is a technology audit and why does your business need one?
How reliable is the technology that your business and its employees rely on each and every day? Every business owner should know the answer to this question.
If you do not have an answer or know that the technology used by your business or organization could be improved, then it may be time for a technology audit, also referred to as an IT audit,[...]
Read more.What is email phishing and why should businesses know about it?
Think about for a moment how many emails you read and send per day. Now, add in the number of emails your coworkers or employees read and send per day.
That’s a lot of emails. Or, as a hacker or other malicious entity may see it, that’s a lot of opportunity for mischief or malicious activity. When it comes to email, that malicious[...]
Read more.Why business WiFi networks fail and how to prevent outages
“The network is down again.”
Those words unleash nightmare scenarios for many business owners and their employees. When networks go down or suffer serious lag in connection speeds, productivity takes a hit and businesses have to scramble to make sure operations don’t grind to a complete halt.
Troubleshooting wireless network[...]
Read more.How to plan for your business's data storage and management needs
All businesses, whether they are small, medium or large, need reliable data storage solutions. There’s no way around it.
Simply think about how much data that is necessary for business operations. There is email, documents, databases, spreadsheets, websites themselves and so much more. All of that data needs to be stored somewhere.
There[...]
Read more.What to do if your small business falls victim to malware
Never before have small businesses needed to focus more on how they plan to defend their networks and devices against cyber attacks, specifically malware.
Most businesses, not just small, are taking this threat seriously - as they should. In 2018, security service investment in company budgets grew faster than any other investment area.
However,[...]
Read more.Here is what businesses need to know about network infrastructure
Business IT needs are always changing. However, one constant that remains is the need for each company to maintain and secure some form of network infrastructure.
It is true that cloud computing’s rise in popularity seems to always be increasing (hint: it is), but many businesses continue to rely on a network infrastructure that is centered[...]
Read more.What businesses should know about wireless network setup
Businesses rely on the internet and the many wireless networking capabilities it offers more than ever before.
With good reason, too. Not only does better wireless networking improve experiences between businesses and customers, but it can also increase capabilities within the office by streamlining communication, offering productivity-boosting[...]
Read more.How to defend your network against common malware types
The world of malware is constantly transforming. Those who wish to cause grief for computer users are always discovering new ways to annoy and even cause actual financial harm through their cyber attacks.
These cyber attacks are also getting sneakier and more sophisticated. On top of that, hundreds of millions of computer viruses and malicious[...]
Read more.Why you shouldn't ignore software updates
Nobody likes interruptions. This is certainly true for businesses and busy professionals who have productivity levels to meet and goals to accomplish every day.
However, some interruptions are necessary. Take software updates, for example. Though they can interrupt the daily workflow, software updates carry anything from user experience[...]
Read more.Don't let your business fall victim to email phishing
If you have an email account, then chances are you have encountered your fair share of phishing and other forms of spam email messages.
Every day, 14.5 billion spam messages are sent, according to Spam Laws. That accounts for 45 percent of all email sent every day.
Email clients apply filters and separate most spam from your general inbox, but[...]
Read more.Why You Should Get a Regular Audit of Your IT Security
Welcome to the Age of Technology, in which everything seems to be connected through the Internet and internal networks. If you are running a business, you most likely have a network that you and your employees use for operational tasks.
Your network might seem secure to you, but how are you really going to know without getting it checked out[...]
Read more.Frequently Asked Questions About Ransomware
Here's what you should know about the KRACK WiFi vulnerability
2. It does not affect Windows or iOS, as they don’t support the part of the handshake that allows for the rekeying vulnerability.
3. BSD/Linux/Android (it runs the Linux kernel) are affected since a majority of the AP’s on the market use[...] Read more.
Why Forcing Frequent Password Changes is Actually Harmful for Security
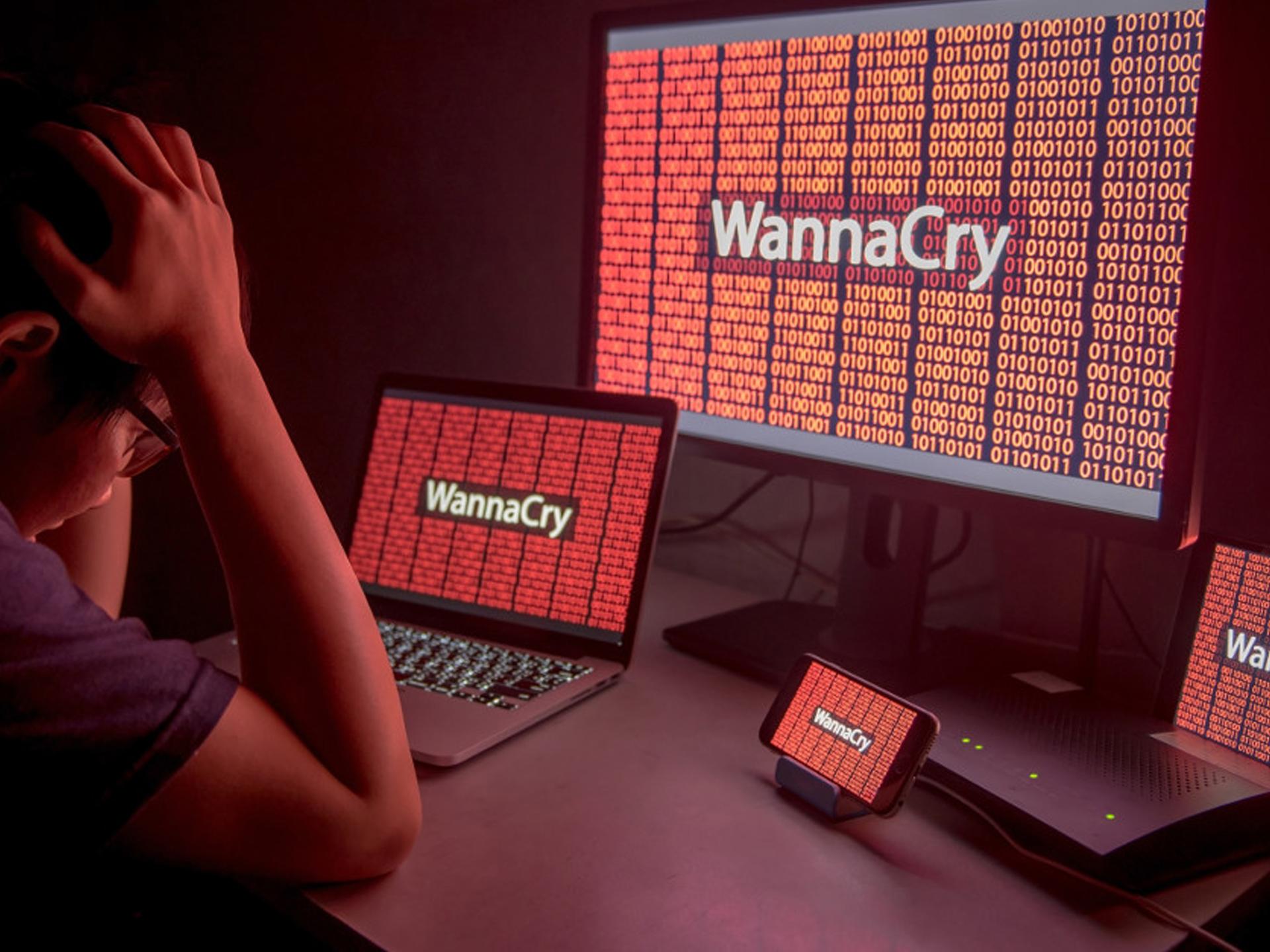
Common Intrusion Points for Ransomware and Malware Infections
As ransomware goes, the WannaCry exploit turned out to[...] Read more.
© Copyright 2017 by Advanced Network Professionals. All Rights Reserved. | Web Design by 154i